In an era of massive digital footprints, transforming public data into actionable intelligence is a crucial skill for any security or investigative professional. The challenge isn't a lack of data, but making sense of it. This is where the best (OSINT) Open Source Intelligence tools come in.
They automate collection and analysis, turning scattered information into clear insights. This guide breaks down the top 10 tools to help you master digital investigation, threat detection, and proactive cybersecurity in 2025 and beyond.
Why are Best OSINT Tools Essential for Cybersecurity Professionals?
The best Open Source Intelligence (OSINT) tools are essential for cybersecurity professionals because they provide the foundational data needed for proactive threat mitigation and robust defense strategies.
By systematically gathering and analyzing publicly available information, security teams can gain critical insights into their organization's external attack surface and potential threats before they escalate.
Open Source Intelligence Tools That Every Researcher Should Know
| Best Open Source Intelligence Tools🛠️ | Key Feature ⭐ | Target Audience 🎯 |
|---|---|---|
| Maltego | Data mapping | Security teams |
| OSINT Framework | Resource hub | Investigators |
| Seon.io | Fraud signals | Fintech ops |
| Shodan | Device index | Pentesters |
| TinEye | Image trace | Creators |
| Lampyre | Link graphs | Threat intel |
| Aircrack-ng | Wi-Fi audit | Ethical hackers |
| BuiltWith | Tech lookup | Sales squads |
| Metagoofil | Metadata scrape | Red teams |
| WolframAlpha | Computed answers | Students |
1. Maltego
Maltego is a premier open-source intelligence platform that empowers investigators by visualising complex data landscapes. It transforms raw data from public sources into clear, interactive graphs, making it easier to see hidden connections between people, companies, and assets.
This tool is indispensable for cybersecurity professionals and law enforcement agencies who need to accelerate their investigations. Maltego maps relationships and uncovers critical insights that would otherwise remain buried in scattered data, turning hours of work into minutes.
Maltego Use Cases and Applications:
Customer Testimonial: “Maltego is a phenomenal data aggregator. It pulls information from countless sources, helping us close complex cases much faster.”
Why Pick Maltego?
For visualising complex data relationships, Maltego is unmatched. It turns abstract data points into actionable intelligence graphs.
2. OSINT Framework
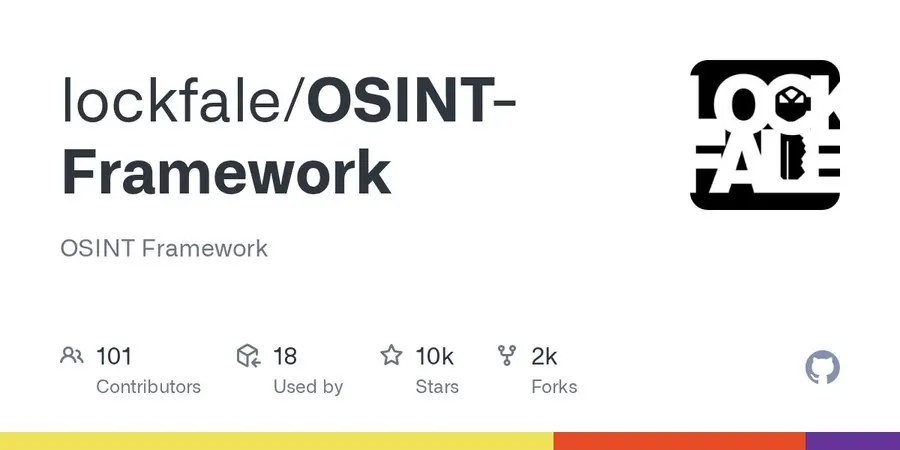
The OSINT Framework acts as a digital library for investigators, neatly organising a vast collection of resources and tools available for open-source intelligence. It provides a structured, web-based interface that categorises tools by function, from username searches to geolocation lookups.
Instead of being a single tool, it is a launchpad that guides both novice and expert analysts to the right resource for their specific task, ensuring a comprehensive and methodical approach to data collection.
OSINT Framework Use Cases and Applications:
Customer Testimonial: “The OSINT Framework is my starting point for every investigation. It’s a comprehensive, well-organised directory that saves me hours.”
Why Pick OSINT Framework?
It's the ultimate free roadmap for any OSINT task, pointing you to the exact tool you need.
3. Seon.io
Seon is a powerful fraud detection platform that leverages OSINT to provide a deep understanding of a user's digital identity. By analysing an email address or phone number, it gathers hundreds of data points from social media and online platforms to generate a highly accurate risk score.
This system is designed for businesses looking to automate their fraud prevention processes. Seon's real-time data enrichment helps stop fraudulent transactions before they happen, safeguarding revenue and building trust with legitimate customers.
Seon.io Use Cases and Applications:
Customer Testimonial: “Seon's digital footprint analysis is incredibly effective. It has significantly reduced our fraud rates with minimal user friction.”
Why Pick Seon.io?
Seon excels at turning a single piece of data, like an email, into a complete fraud risk profile.
4. Shodan
Often called the “search engine for hackers,” Shodan is a unique tool that scans the internet to identify and index connected devices. Unlike Google, it finds servers, webcams, IoT devices, and industrial control systems, providing detailed information on their configuration and potential vulnerabilities.
For cybersecurity teams and penetration testers, Shodan is an essential tool for reconnaissance. It offers an unparalleled view of an organisation's external attack surface, revealing exposed ports, misconfigured services, and insecure devices that could be exploited.
Shodan Use Cases and Applications:
Customer Testimonial: “With Shodan, we discovered an exposed server we didn't know we had, allowing us to secure it immediately.”
Why Pick Shodan?
Shodan provides unmatched visibility into internet-connected devices, making it essential for mapping any organisation's digital footprint.
5. TinEye
TinEye is a specialised reverse image search engine designed for accuracy and comprehensiveness. It excels at tracking where an image appears online, how it has been modified, and if older versions exist. Its proprietary technology makes it a go-to tool for content creators and investigators.
By focusing purely on image matching, TinEye provides results that are often more precise than general-purpose search engines. It's an invaluable resource for anyone needing to verify the origin of an image or protect their visual content from unauthorised use.
TinEye Use Cases and Applications:
Customer Testimonial: “TinEye is my first stop for verifying images. Its ability to track an image's history is incredibly reliable.”
Why Pick TinEye?
For fast, accurate, and comprehensive reverse image searching, TinEye's focused technology delivers superior results for content verification.
6. Lampyre
Lampyre is a premium, all-in-one OSINT application built for in-depth data analysis and visualisation. Starting with a single data point like a name or phone number, it automatically queries over 200 data sources to uncover and map hidden connections.
Designed for cyber threat intelligence, financial analytics, and criminal investigations, Lampyre presents its findings in intuitive graphs. This simplifies the process of untangling complex networks of relationships between individuals, organisations, and digital assets, making it a powerhouse for professional analysts.
Lampyre Use Cases and Applications:
Customer Testimonial: “Lampyre's ability to automatically pull from hundreds of sources and graph the results has been a game-changer for our investigations.”
Why Pick Lampyre?
Lampyre excels at deep data analysis, automatically turning one data point into a complete intelligence picture with visualisations.
7. Aircrack-ng

Aircrack-ng is a comprehensive suite of command-line tools used by cybersecurity professionals to assess Wi-Fi network security. It focuses on monitoring, attacking, testing, and cracking wireless protocols, including WEP, WPA, and WPA2-PSK.
This tool is a staple for ethical hackers and penetration testers conducting wireless security audits. It allows them to capture network packets, test the strength of Wi-Fi passwords, and execute various attacks to identify vulnerabilities before malicious actors can exploit them.
Aircrack-ng Use Cases and Applications:
Customer Testimonial: “Aircrack-ng is the industry standard for Wi-Fi pentesting. It's powerful, reliable, and essential for any wireless security audit.”
Why Pick Aircrack-ng?
For hands-on Wi-Fi security testing, Aircrack-ng provides an unmatched, powerful toolkit for cracking and analysing wireless networks.
8. BuiltWith
BuiltWith is a business intelligence tool that provides detailed profiles of the technology used on websites. It can identify a site's content management system, analytics tools, frameworks, and advertising partners, offering a complete picture of its technology stack.
This information is a goldmine for sales teams, marketers, and researchers. By understanding what technologies a potential client or competitor is using, businesses can tailor their sales pitches, conduct targeted market research, and gain a significant competitive edge.
BuiltWith Use Cases and Applications:
Customer Testimonial: “BuiltWith gives us the exact tech intelligence we need to find qualified prospects. It's an indispensable tool for our sales team.”
Why Pick BuiltWith?
BuiltWith offers unparalleled insight into any website's technology stack, making it perfect for lead generation and competitive analysis.
9. Metagoofil

Metagoofil is a highly specialised OSINT tool designed to extract metadata from public documents available on a target website.
It searches for files like PDFs, Word documents, and spreadsheets, then analyses them to uncover hidden information.
This metadata can include usernames, software versions, network paths, and email addresses, which is incredibly valuable for penetration testers during the initial reconnaissance phase. Metagoofil automates the process of finding and mining these documents for intelligence that can be used to map out a target's internal structure.
Metagoofil Use Cases and Applications:
Customer Testimonial: “Metagoofil is fantastic for the reconnaissance phase. It quickly extracts valuable metadata from public files that we can use.”
Why Pick Metagoofil?
Metagoofil is a master at one thing: extracting critical intelligence hidden within the metadata of publicly available documents.
10. WolframAlpha
WolframAlpha stands apart as a “computational knowledge engine” rather than a traditional search engine. It's an exceptional tool for students and researchers because it doesn't just find web pages; it computes answers to questions using its vast repository of curated, expert-level data.
From solving complex calculus problems to providing detailed socioeconomic data for a research paper, WolframAlpha delivers precise, factual answers. This makes it an invaluable academic resource for checking homework, exploring complex topics, and getting instant, reliable information without sifting through search results.
WolframAlpha Use Cases and Applications:
Customer Testimonial: “WolframAlpha is my go-to for my university assignments. It provides accurate, computed answers that save me hours of research.”
Why Pick WolframAlpha?
WolframAlpha computes expert-level answers on demand, making it an essential academic tool for students seeking factual, reliable information.
Understanding the Core Function of OSINT Tools in Data Collection
The core function of Open Source Intelligence (OSINT) tools in data collection is to automate the process of finding, gathering, and indexing information from a vast array of public sources.
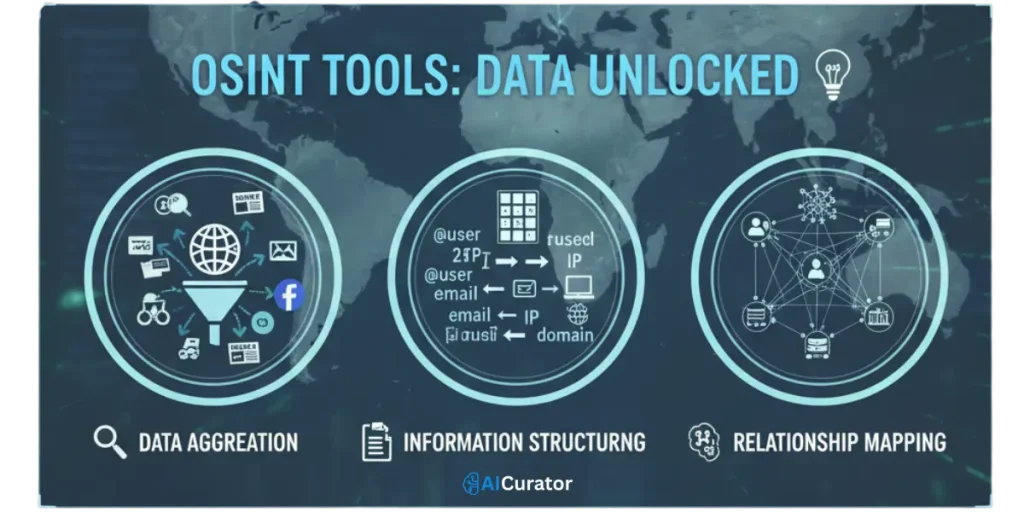
These tools transform a manual, time-consuming process into an efficient and scalable operation, allowing analysts to focus on analysis rather than data acquisition.
The Strategic Value of OSINT
In summary, the right OSINT tools are game-changers for cybersecurity professionals, threat analysts, and investigators.
They transform the overwhelming sea of public data into clear, actionable intelligence, revealing hidden connections and digital footprints.
From automated reconnaissance to deep data visualisation, these solutions provide the insights needed to secure assets and conduct thorough investigations. If you are looking to enhance your intelligence-gathering capabilities, we encourage you to explore the options discussed. Choose the right tool to elevate your workflow and achieve your objectives.
Recommended Readings: